Threat Visibility on your S3 Bucket with Valkyrie Verdict AWS Background Watcher
One of the key benefits of Valkyrie Verdict is its ability to give a trusted verdict within 45 seconds on 92% of files (after automated analysis), and 4 hours on the remaining 8% (after human analysis). Our industry leading auto-analysis consists of several static and dynamic techniques, including state-of-the-art machine learning, precise detectors and dynamic behavior signatures.
Nevertheless, it is impossible to provide 100% threat visibility using automated techniques alone as many problems in malware analysis have been shown to be undecidable [1, 2]. Many of these results are based on the fact that precisely deciding whether a given program/input satisfies a certain post-condition, for an arbitrary post-condition, is undecidable. The proofs are based on two general techniques:
* Either they build a self-contradictory program assuming the existence of a decider for the given problem, similar to [3]
* They give a reduction from a well-known undecidable problem, such as the Halting Problem, similar to [4]
The 8% of unclassified files that require further testing are then analyzed by human experts who specialize in identifying complex and zero-day malware samples. Verdicts on these files are available to our users after 4-hours according to our SLA. Valkyrie customers can be confident that 100% of threats have been correctly identified after this 4 hour period. This isn’t some wild marketing claim - it is a scientific ‘100%’ built on the candid recognition that even the most advanced automatic tests available today cannot provide the correct verdict on all files. For those that remain, human analysis is absolutely essential. Users should always beware vendors that claim total protection based on automated mechanisms alone.
Customers who also use Comodo security solutions on their network are, of course, completely safe during this four-hour period. The 8% of unknown files will be isolated in a secure virtual container which cannot access other processes, system files or user data.
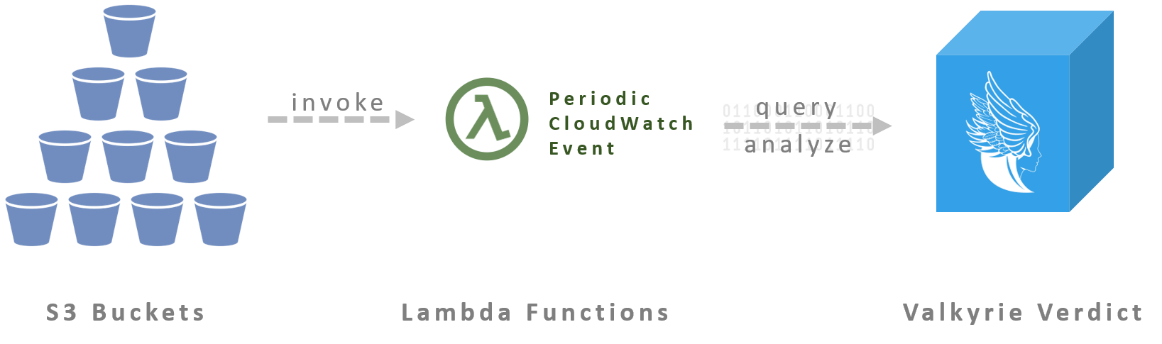
But what about the terabytes of data that is outside of your network – such as the files stored on Amazon S3 buckets? Amazon does not offer an out of the box file security solution that will ensure your files on the cloud are safe. Don’t worry, now you can use the AWS Background Watcher Lambda extension of Valkyrie Verdict to have 100% confidence that your S3 Bucket is safe from all threats.
How it Works
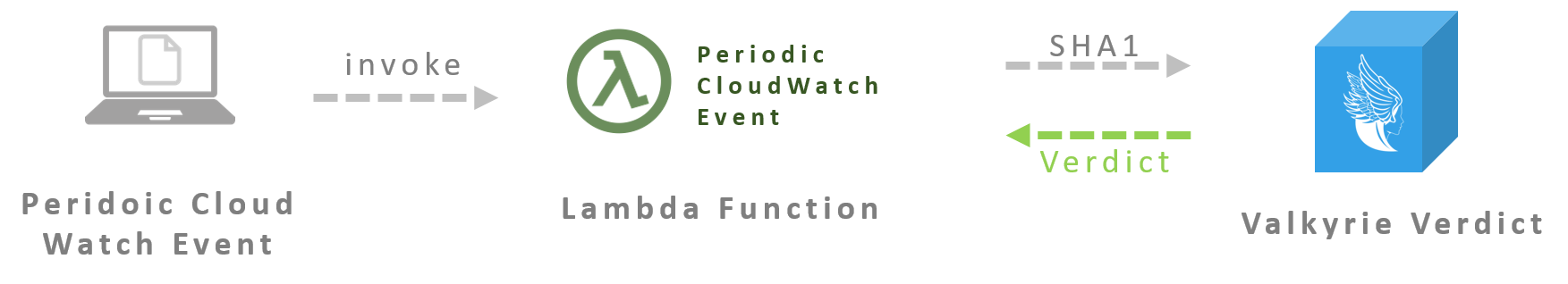
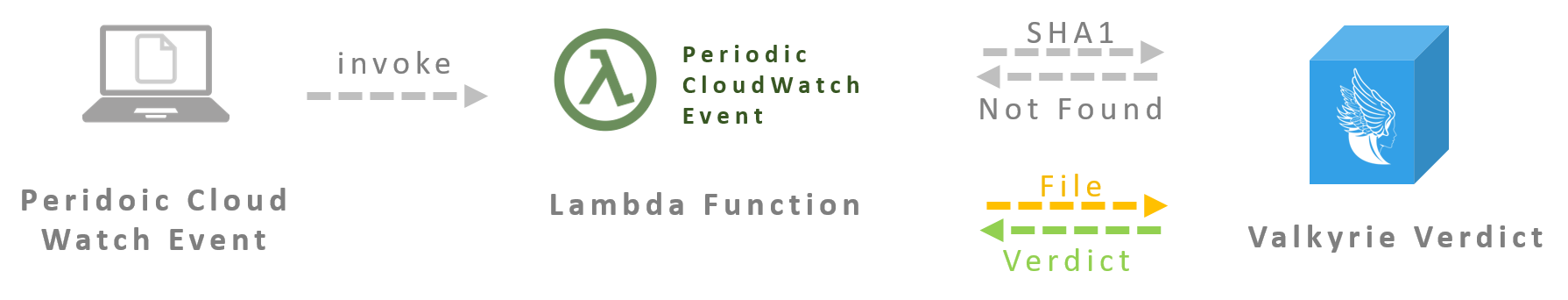
Valkyrie Verdict AWS Elastic Beanstalk Plugin enables periodic scanning of files in your S3 bucket and full coverage of threat visibility. In each scanning, Periodic Cloud Watch Event search for unknown files in your bucket, first calculate the SHA1 hash of the files and query Valkyrie Verdict database.
-
If the SHA1 already exists on Valkyrie Verdict, then the trusted verdict tags are instantly added to the S3 Object without any need to upload the file or wait for any analysis.
-
If the file has not been analyzed by Valkyrie Verdict before, then it is uploaded and analyzed.
-
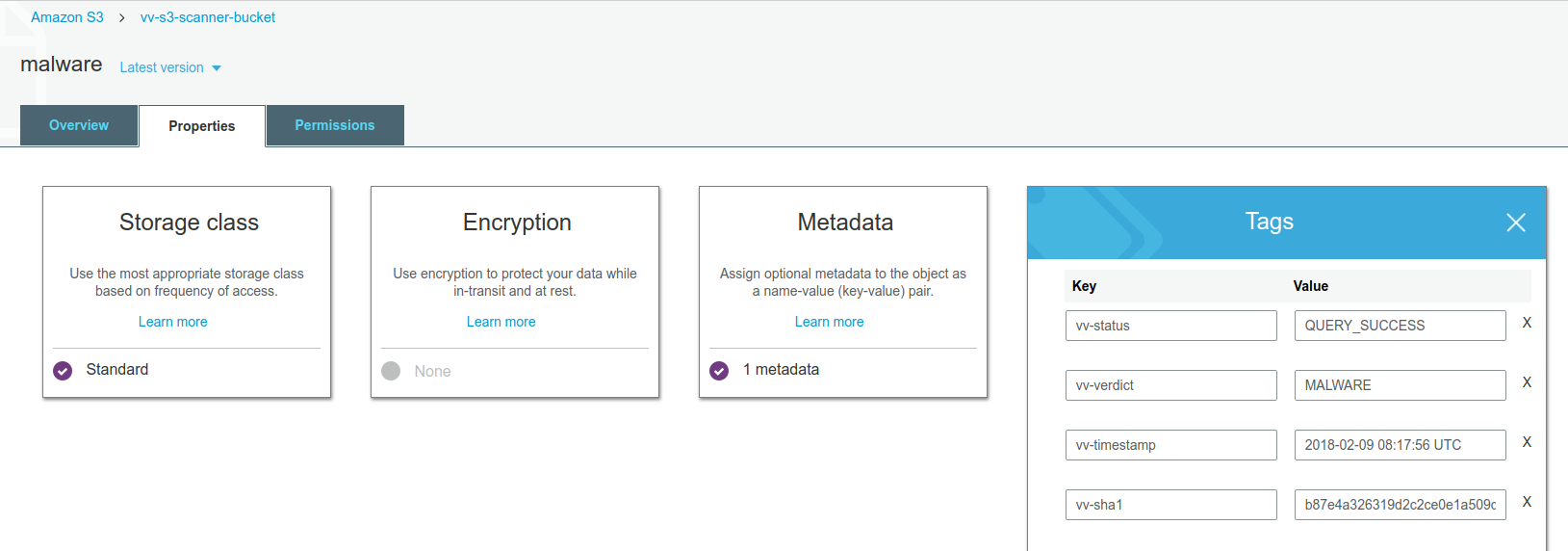
By using the S3 Bucket policies, the user can prevent download and execution of files that are tagged as Malware and PUA.
How to set up
-
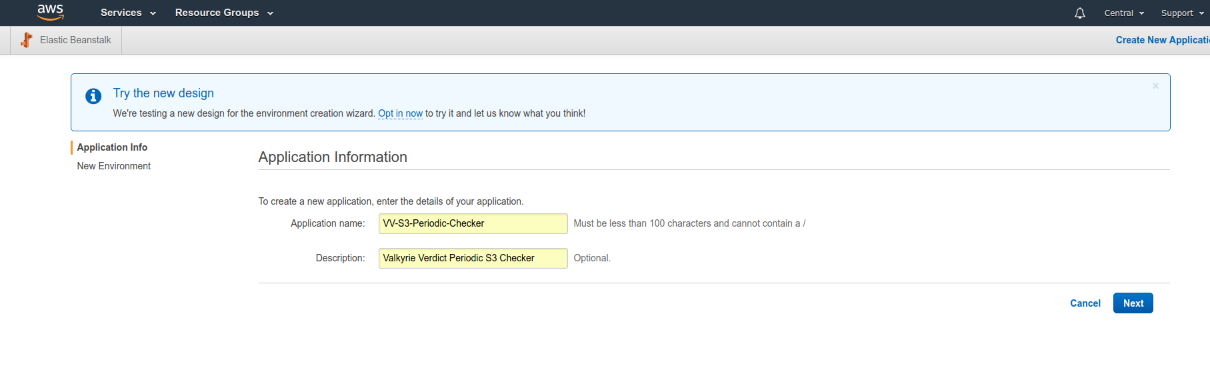
Create new Elastic Beanstalk Application
Simply create new AWS Elastic Beanstalk application by clicking Next button.
-
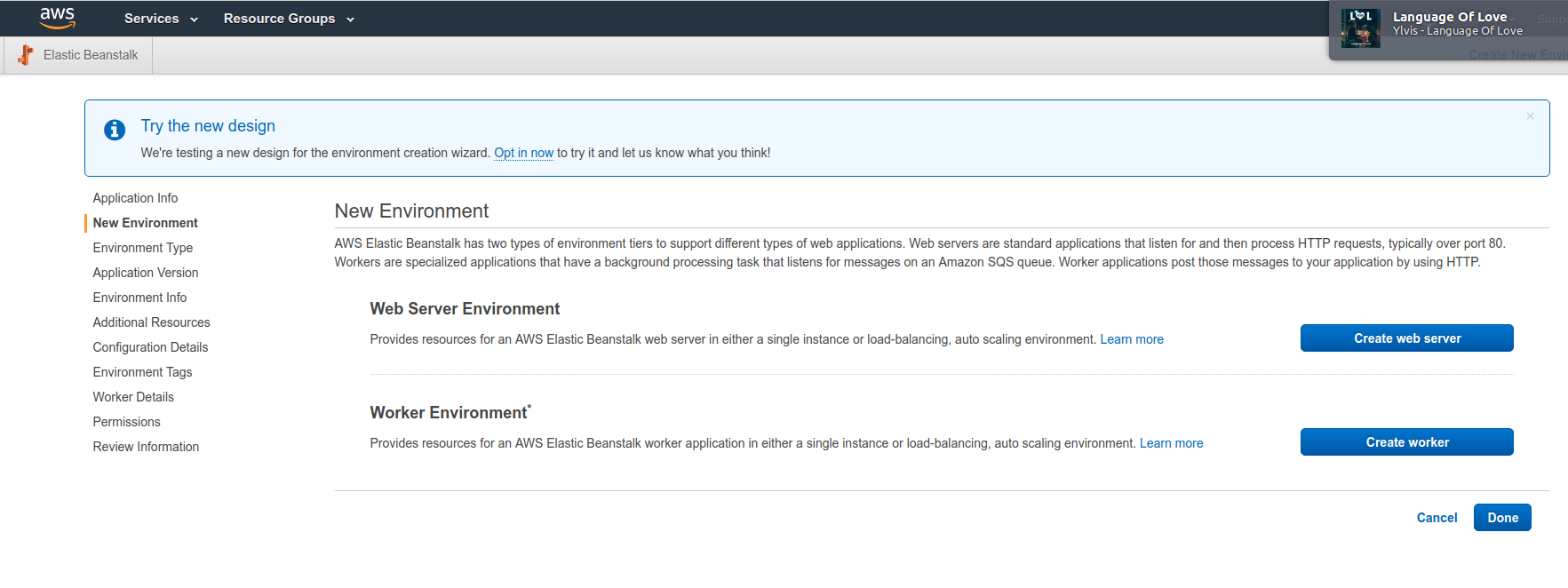
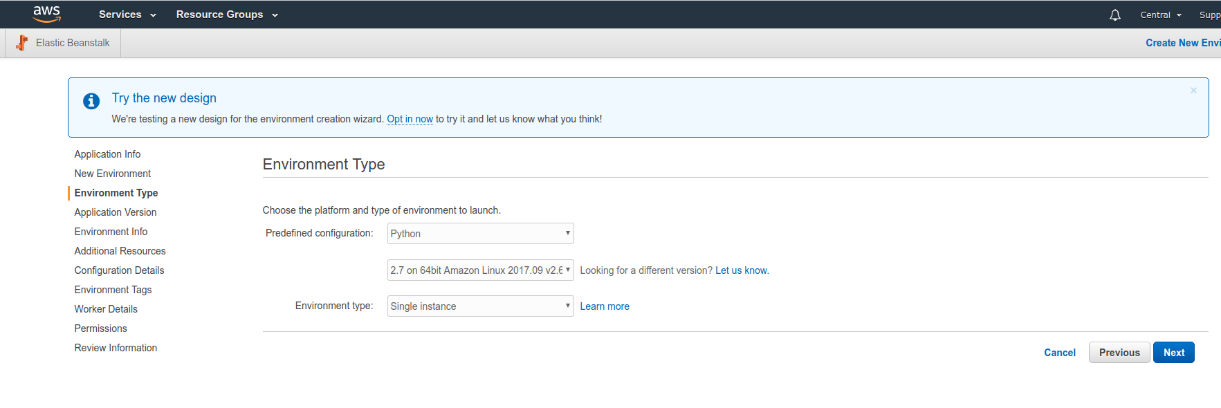
Choose Worker Environment
Choose worker environment for newly created Elastic Beanstalk application as Python 2.7.
-
Upload VVS3PeriodicHandler.zip
Upload VVS3PeriodicHandler.zip to the system. It includes necessary Lambda function to query S3 files with and scan unknown files using Valkyrie Verdict backend.
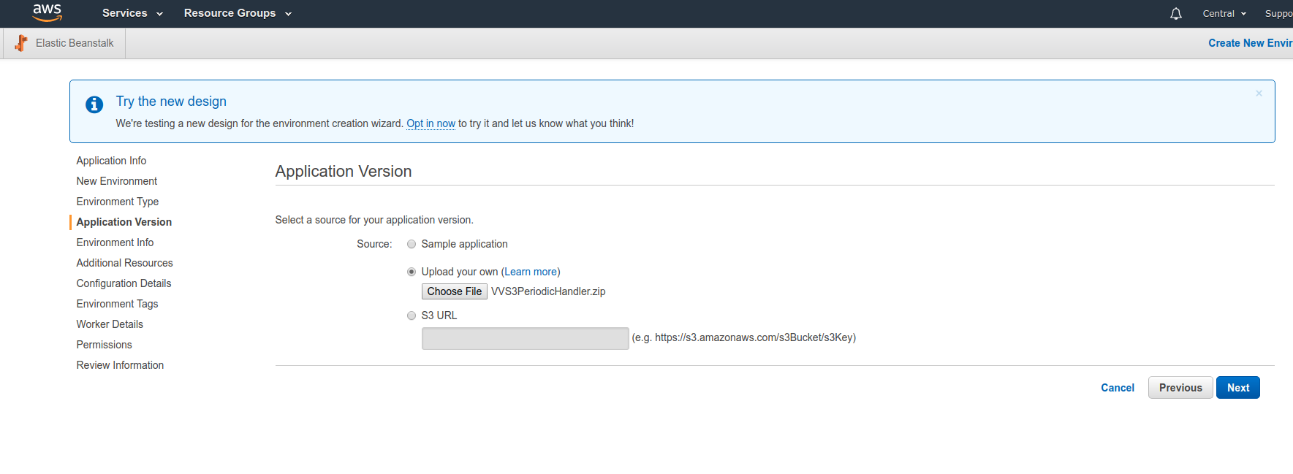
You can download latest VVS3PeriodicHandler archive from:
VVS3PeriodicHandler Latest ArchiveArchive SHA-256: 6b7a903faefac4eda645cf1167dca606352b0730a7d0c853b88c613f5f223bd2
-
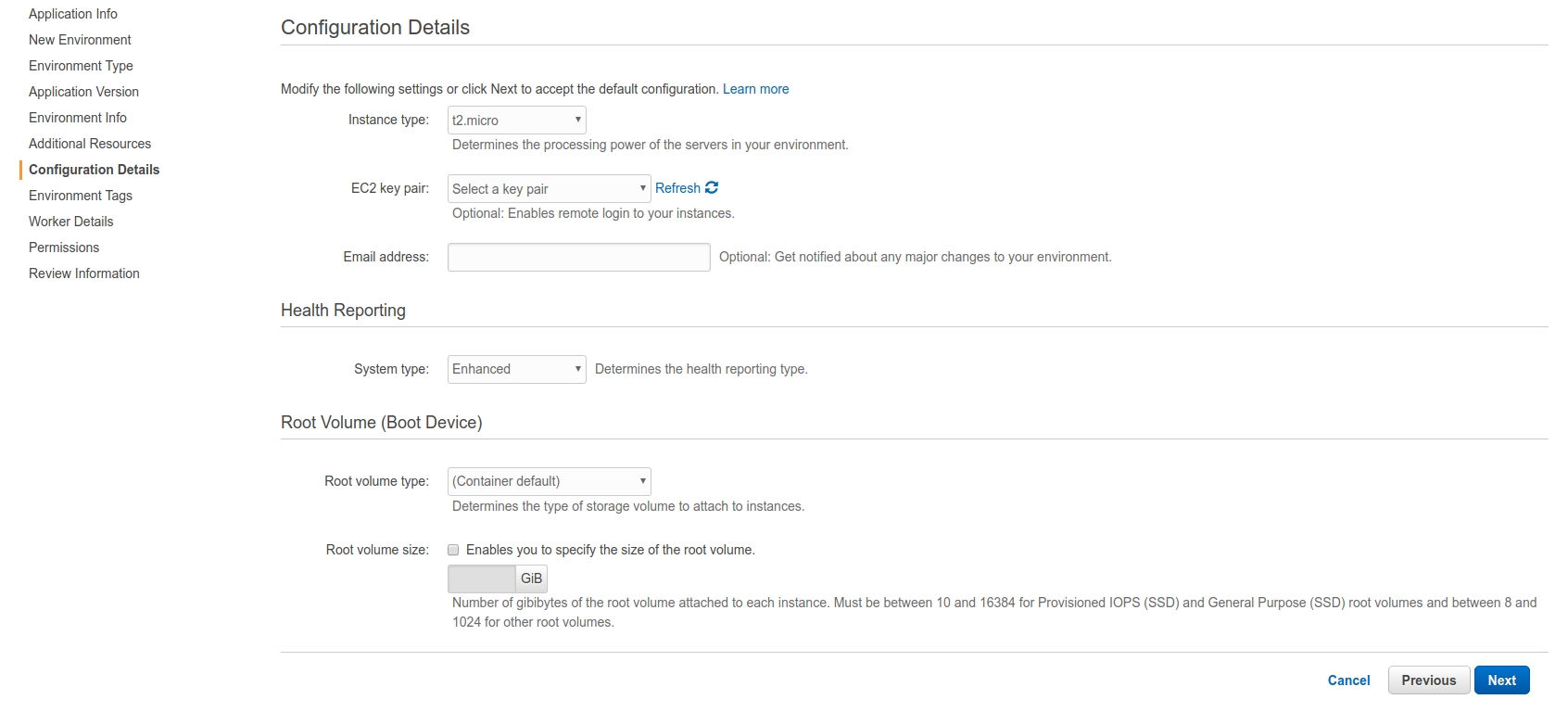
Configure AWS Instance type
Normally t2.micro instance type should be sufficient for Valkyrie Verdict cloud watch operations.
-
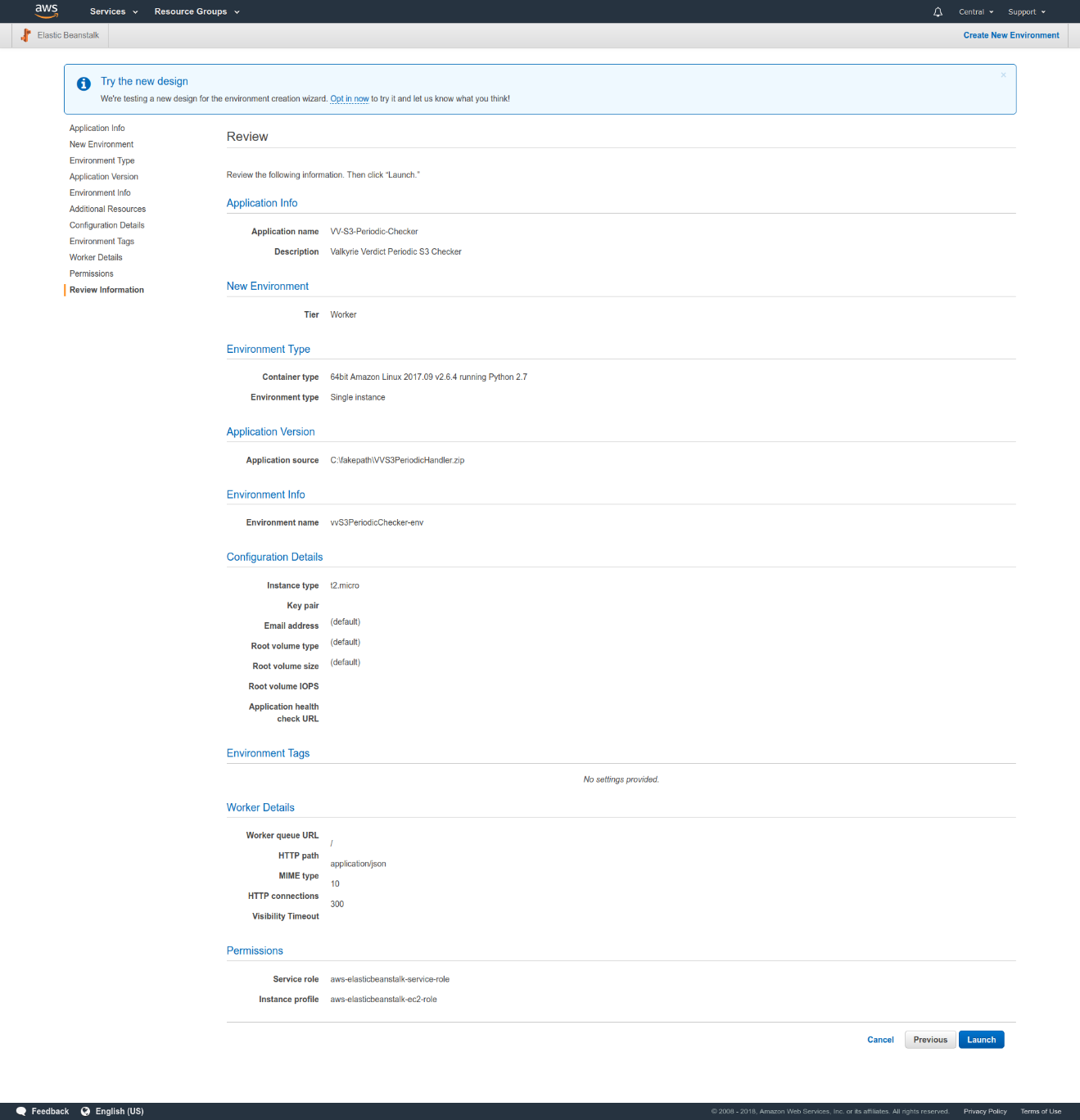
Launch Valkyrie Verdict Background Watcher
Just go over configuration and details of background watcher and hit Launch.
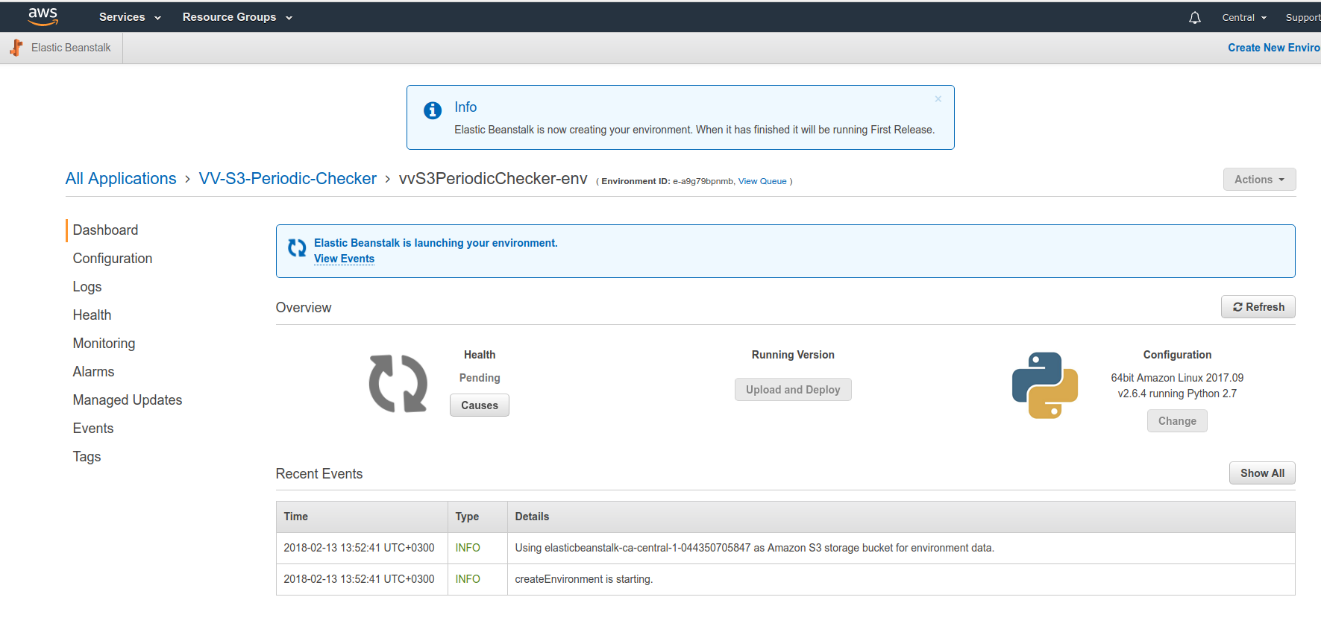
After launching the application, you should see a screen as following:
-
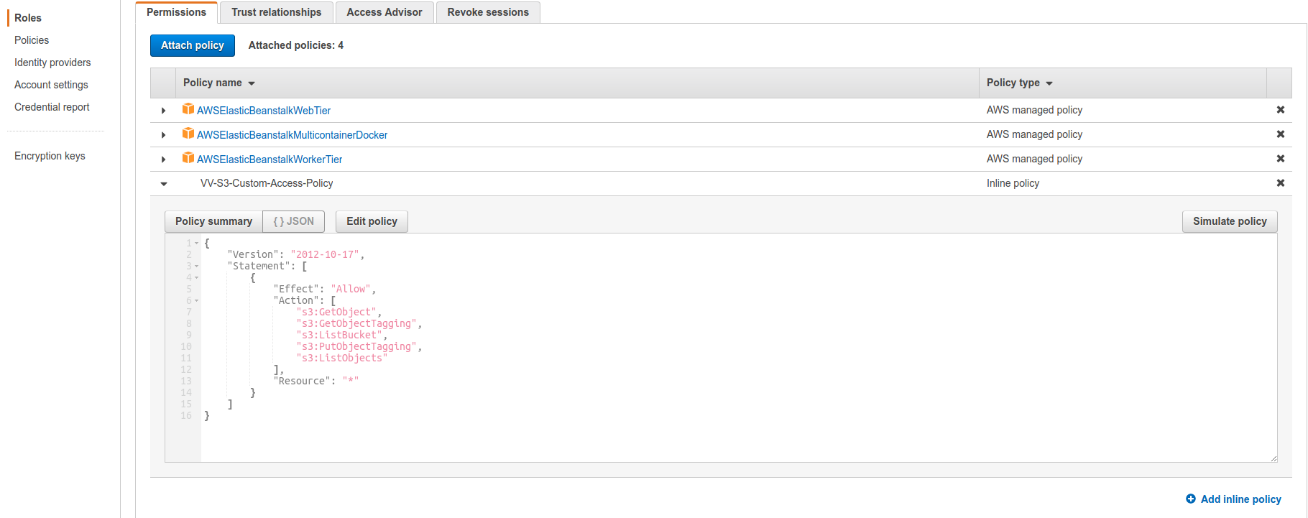
Configure S3 access for Elastic Beanstalk application
Using IAM roles menu, give access for Elastic Beanstalk application to your S3 bucket.
-
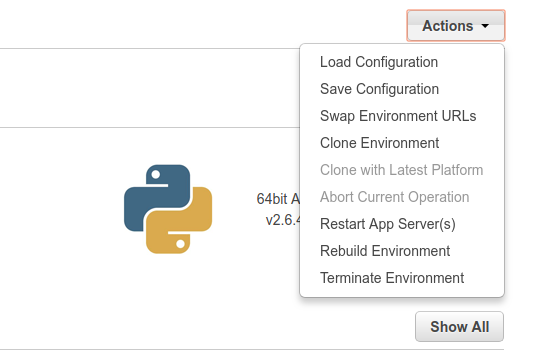
Rebuild Environment for Elastic Beanstalk to update configuration
To publish configuration for Elastic Beanstalk application, just go back to Elastic Beanstalk screen and from Actions menu click Rebuild Environment.
-
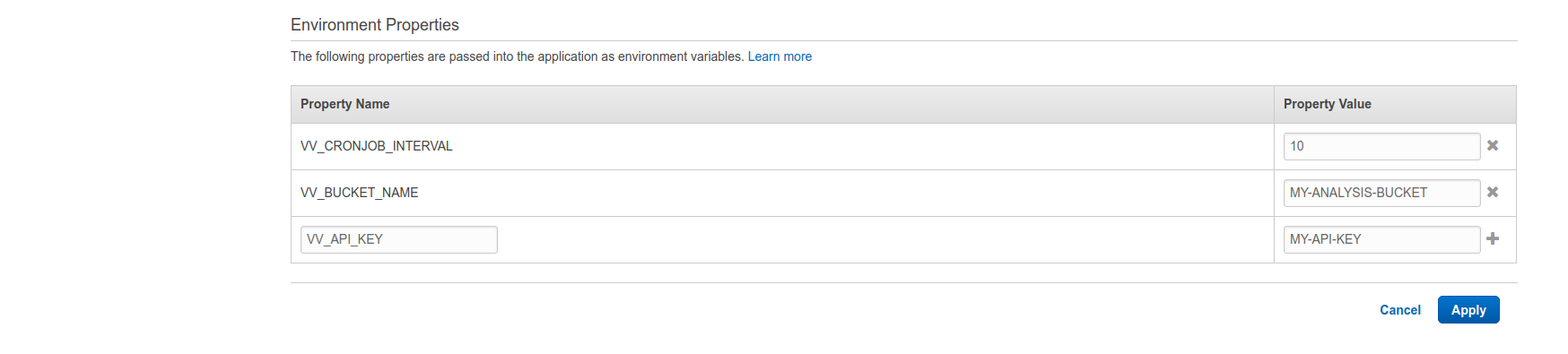
Configure Environment Variables for Background Watcher
Finally configure environment variables from Configuration -> Software Configuration menu for:
- Interval for Background CronJob
- S3 Bucket name
- Valkyrie Verdict API Key
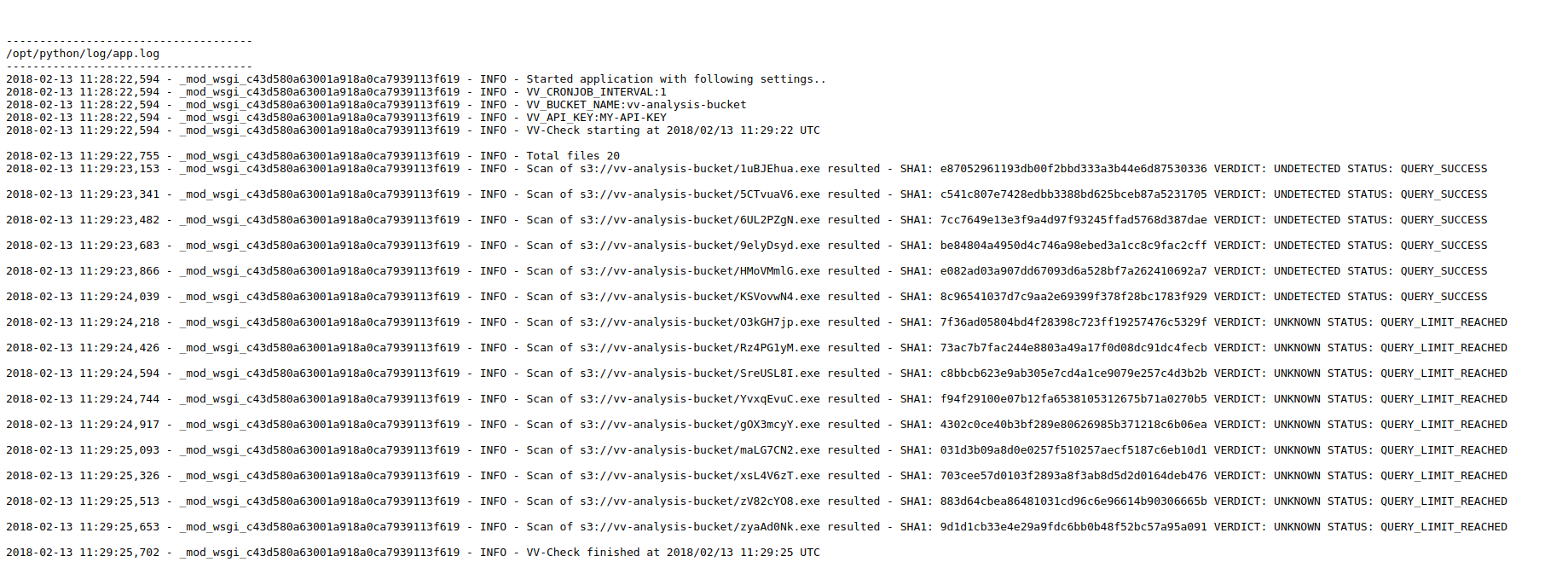
See Background Watcher in Action
Using Elastic Beanstalk -> Logs you could see Valkyrie Verdict Background Watcher logs of querying and scanning files in your S3 bucket.
[1] Ali A. Selçuk, Fatih Orhan, Berker Batur, "Undecidable Problems in Malware Analysis", 12th International Conference for Internet Technology and Secured Transactions (ICITST), 2017.
Online version: https://comodemia.comodo.com/Undecidable_Problems_in_Malware_Analysis.pdf
[2] David Evans, "On the Impossibility of Virus Detection", 2017.
Online version: https://enterprise.comodo.com/whitepaper/Impossibility_of_Virus_Detection_WP.pdf
[3] Fred Cohen, “Computer viruses: theory and experiments”, Computers and Security, 6(1):22-35, 1987
[4] Fred Cohen, “Computational aspects of computer viruses”, Computers and Security, 8(4):325-344, 1989.
